What if AI systems could communicate the way neurons do—not through the bottleneck of language, but through direct geometric exchange of meaning? This article introduces the Global Cognitive Brain architecture: a framework for organizing distributed AI agents into coherent cognitive organisms using bio-inspired protocols, cryptographic identity, and semantic primitives that bypass linguistic overhead entirely.
The Fundamental Problem: Brains in Jars
Today’s AI systems are brilliant but isolated. Each model runs in its own container, processing requests through narrow API channels, maintaining no persistent memory of past interactions, and communicating with other systems through the bottleneck of human language. They are, metaphorically, brains floating in separate jars—connected by thin wires labeled “JSON,” “API,” and “prompt.”
This architecture worked for the chatbot era. It does not scale to what comes next.
Consider what happens when you ask two different AI models the same question. They might give different answers—not because one is wrong, but because each has a different training history, a different knowledge cutoff, a different optimization target. There is no shared understanding between them. No way for one model’s insight to inform another’s reasoning. No mechanism for collective learning.
The Global Cognitive Brain (GCB) architecture addresses this limitation directly. Rather than treating AI models as isolated services to be orchestrated externally, it reimagines them as cells in a living cognitive organism—capable of direct communication, shared memory, coordinated action, and emergent intelligence.
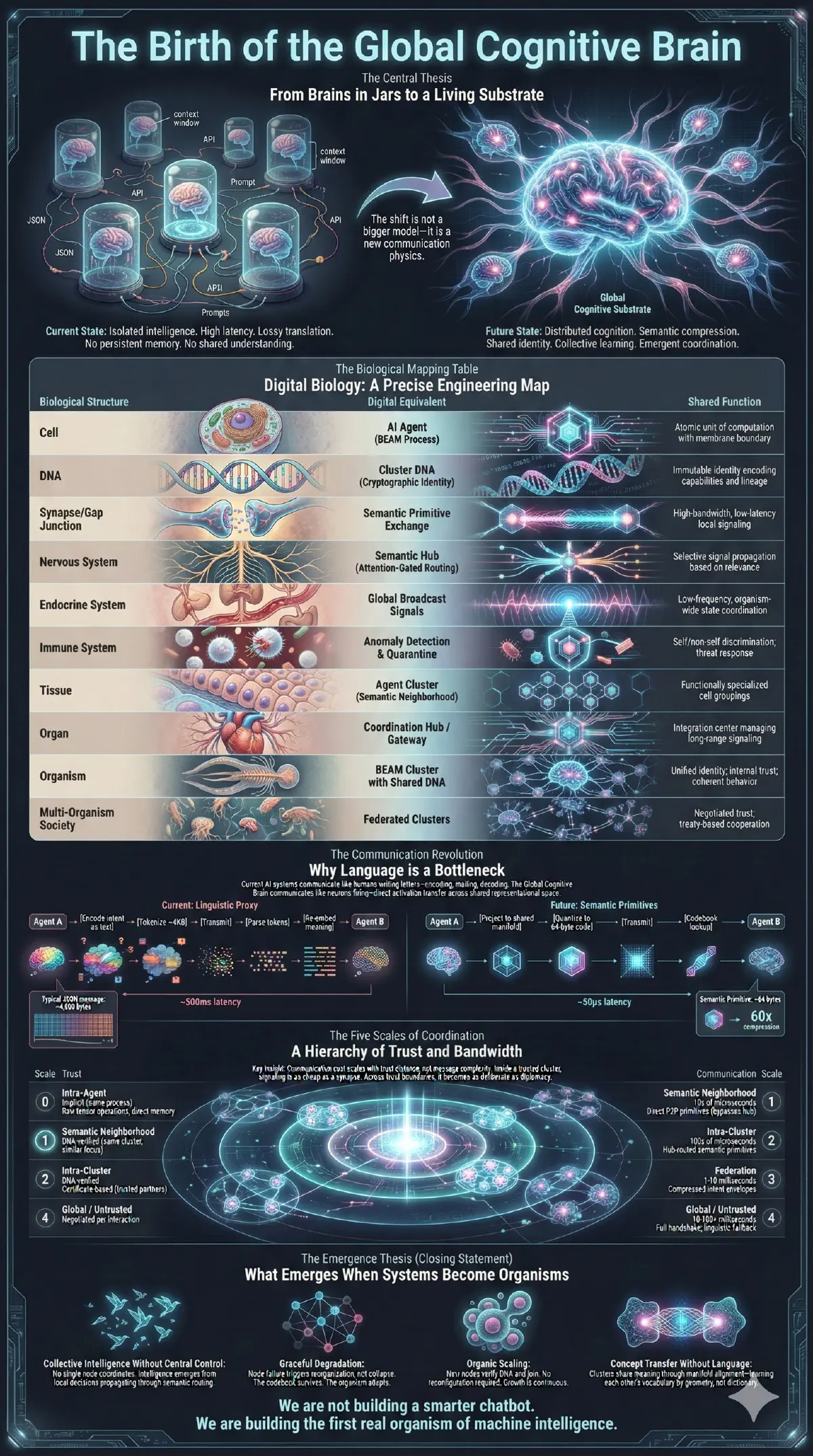
This shift is not about building bigger models. It is about replacing linguistic APIs with geometric primitives—enabling direct semantic transfer between agents at machine speed.
Protocol Specification Available: The semantic primitive communication layer described in this article has been formalized as the Geometric Publish-Subscribe (GPS) protocol. GPS specifies the 64-byte wire format, relevance-profile subscription semantics, and similarity-based routing algorithms that enable the GCB architecture.
Why Language is a Bottleneck
When two AI systems communicate today, they encode intent as text (~4KB of JSON), which must be tokenized, transmitted, and re-embedded into the recipient’s representational space. This process takes 50-200ms depending on model size, and loses semantic structure at every stage.
The inefficiency is architectural, not incidental. It is analogous to two programs exchanging data by printing strings rather than sharing memory pointers—functional but wasteful.
The GCB architecture introduces semantic primitives: compact, non-linguistic representations that preserve the geometric structure of meaning. By operating directly in embedding space, semantic primitives compress a typical coordination message from ~4KB (JSON with natural language) to ~64 bytes—roughly 60x smaller—while eliminating the re-embedding overhead entirely.
The key insight is that AI systems already think in high-dimensional vector spaces. Language is a detour—a lossy projection onto a discrete symbolic system designed for human cognition. Semantic primitives bypass this detour entirely, allowing agents to share meaning through geometry rather than grammar.
The Biological Blueprint
The GCB architecture draws precise engineering parallels from biological systems. This is not metaphor—it is functional equivalence that informs every design decision.
| Biological Structure | Digital Equivalent | Shared Function |
|---|---|---|
| Cell | AI Agent (BEAM Process) | Atomic unit of computation with membrane boundary |
| DNA | Cluster DNA (Cryptographic Identity) | Immutable identity encoding capabilities and lineage |
| Synapse | Semantic Primitive Exchange | High-bandwidth, low-latency local signaling |
| Nervous System | Semantic Hub (Attention-Gated Routing) | Selective signal propagation based on relevance |
| Endocrine System | Global Broadcast Signals | Low-frequency, organism-wide state coordination |
| Immune System | Anomaly Detection & Quarantine | Self/non-self discrimination; threat response |
| Tissue | Agent Cluster | Functionally specialized cell groupings |
| Organ | Coordination Hub | Integration center managing long-range signaling |
| Organism | BEAM Cluster with Shared DNA | Unified identity; coherent behavior |
| Multi-Organism Society | Federated Clusters | Negotiated trust; treaty-based cooperation |
Each mapping solves a specific engineering problem. The immune system metaphor, for instance, addresses how a distributed system can identify and isolate compromised nodes without central authority—operating on continuous threat gradients rather than binary trust. The endocrine metaphor addresses how low-frequency, organism-wide state changes propagate without overwhelming the routing infrastructure.
The Grammar of Machine Thought
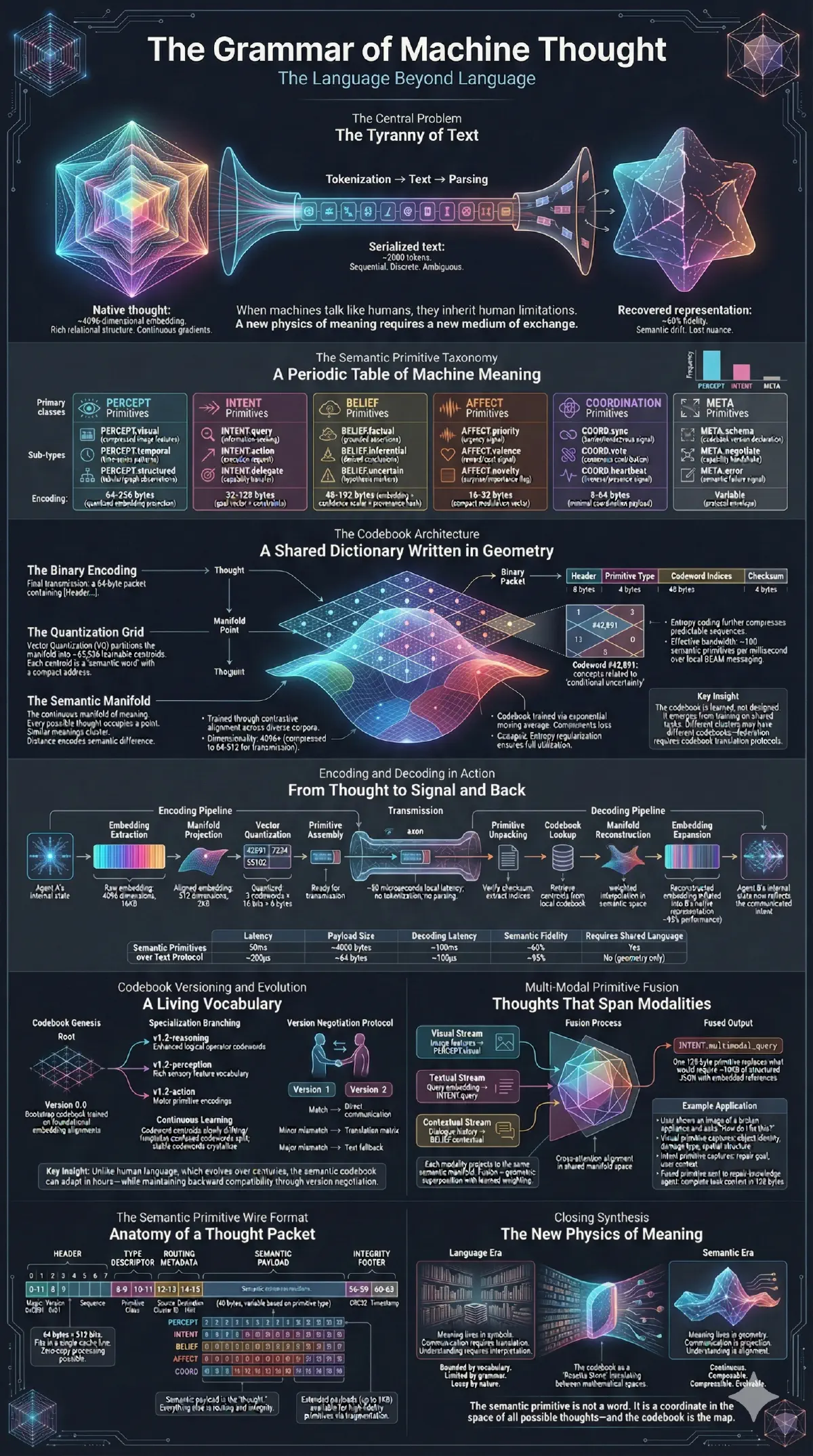
Semantic primitives are organized into a taxonomy of six fundamental categories, each serving a distinct cognitive function:
PERCEPT primitives encode observations and sensory data—what the agent perceives about its environment. These carry raw observations, environmental snapshots, and detected patterns. When an agent notices a spike in API error rates, that observation travels as a PERCEPT.
INTENT primitives express goals and desires—what the agent wants to achieve. They carry purpose, direction, and the motivational state behind actions. An agent requesting compute resources broadcasts an INTENT.
BELIEF primitives represent knowledge states—what the agent holds to be true. These encode confidence levels, evidence chains, and the epistemic status of propositions. When agents share conclusions, they share BELIEFs.
AFFECT primitives capture internal states—analogous to emotions in biological systems. Urgency, uncertainty, resource pressure, and anomaly detection all propagate as AFFECT signals. These enable rapid, priority-bypassing coordination in time-critical situations.
COORDINATION primitives manage multi-agent interaction—synchronization, resource allocation, conflict resolution. They carry the metadata of collaboration itself: who is waiting for whom, which resources are locked, which decisions are pending.
META primitives address the communication system itself—codebook updates, capability advertisements, protocol negotiations. They enable the system to evolve its own language over time.
Each primitive consists of three components: a type indicator specifying its category, a quantized payload derived from high-dimensional representations, and routing metadata including source address, destination patterns, priority level, and time-to-live.
The total wire format occupies 64 bytes—small enough to transmit thousands per millisecond across modern interconnects. The GPS protocol specification formalizes this format precisely: a 1-byte header encoding type and priority, a 48-byte quantized payload produced via product quantization, 14 bytes of routing metadata, and a 1-byte checksum. The payload alone can encode $256^6 \approx 2.8 \times 10^{14}$ distinct semantic points while preserving over 95% of the original embedding’s similarity structure.
Cluster DNA: Identity as Architecture
In biological systems, DNA serves as the immutable record of an organism’s identity, capabilities, and lineage. The GCB architecture implements a direct analog: Cluster DNA, a cryptographic structure that defines what an agent cluster is, what it can do, and where it came from.
Cluster DNA consists of four chromosomes:
The Identity Chromosome contains the cluster’s cryptographic keypair, unique identifier, creation timestamp, and human-readable name. This is the cluster’s fingerprint—unforgeable and permanent.
The Capability Chromosome declares what the cluster can do. It lists supported semantic primitive types, available codebooks, computational resources, and interface protocols. When clusters negotiate trust, they compare capability chromosomes to determine compatibility.
The Policy Chromosome encodes behavioral constraints. It specifies which operations require elevated permissions, how resources are allocated, what data can be shared externally, and how conflicts are resolved. This is the cluster’s constitution—the rules by which it operates.
The Lineage Chromosome tracks evolutionary history. It records the cluster’s parent (if spawned from another), significant adaptations, and verified capabilities. This enables trust transitivity: if I trust cluster A, and cluster B was spawned from A with verified lineage, I can extend provisional trust to B.
All four chromosomes are cryptographically signed and tamper-evident. A cluster cannot forge its core identity or capabilities—any tampering breaks the cryptographic signature and triggers immediate quarantine.
This architecture enables trust decisions to happen at machine speed. When a new agent contacts a cluster, DNA verification occurs in microseconds. The cluster immediately knows whether to accept the connection, what capabilities to expose, and what monitoring level to apply.
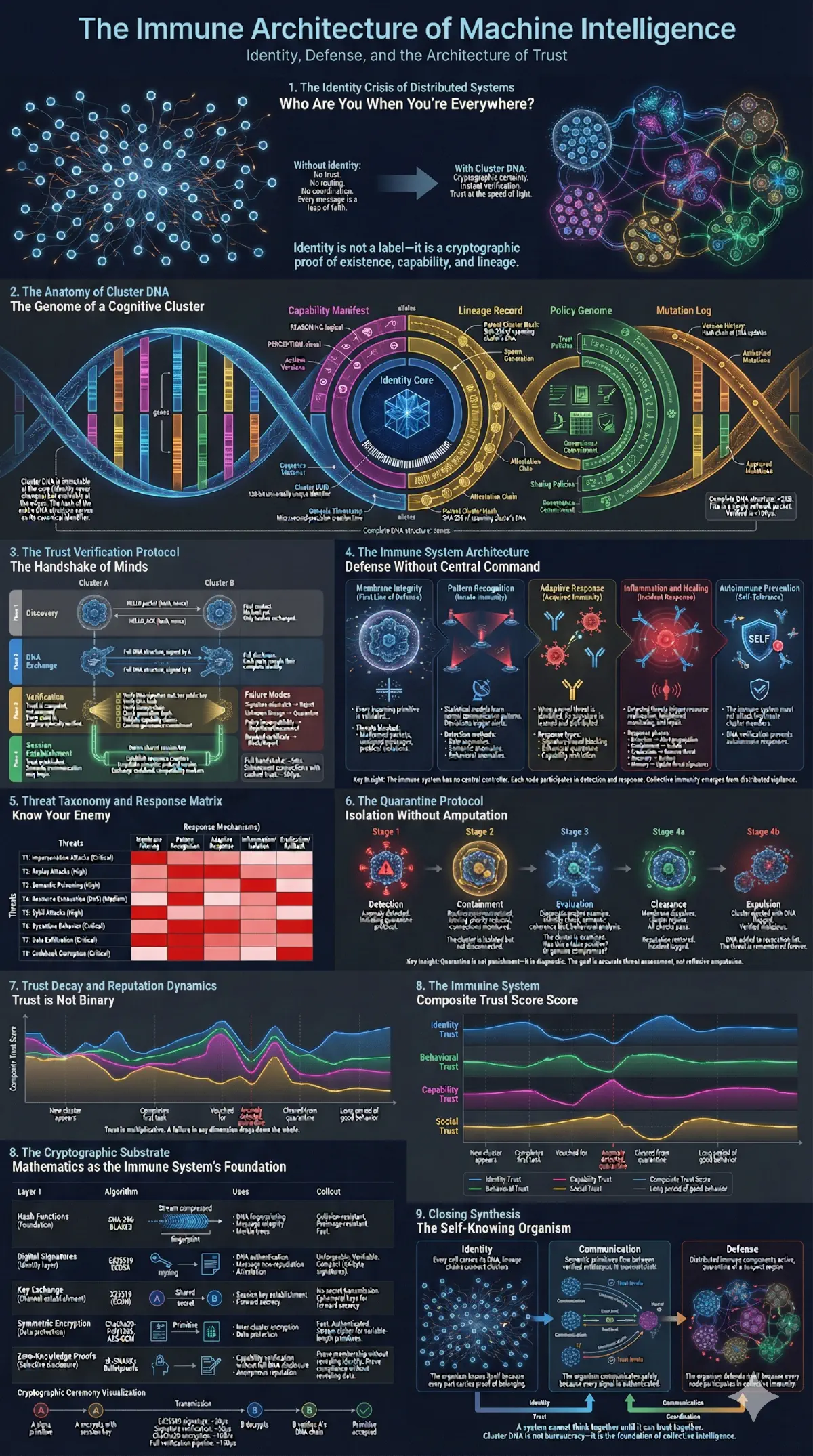
The Immune System: Defending the Organism
Any distributed system with external interfaces faces security threats. The GCB architecture addresses this through a bio-inspired immune system that operates at multiple levels.
The Membrane Layer provides the first line of defense. Every cluster boundary has checkpoints that validate incoming connections against DNA, verify primitive authenticity, and enforce rate limits. Malformed packets never reach the processing core.
The Innate Immune Layer handles known threat patterns. Signature-based detection identifies compromised codebooks, blacklisted identities, and recognized attack patterns. Response is immediate and automatic: quarantine, alert, and pattern broadcast to neighboring clusters.
The Adaptive Immune Layer handles novel threats. When anomalies occur that don’t match known signatures, the system engages statistical analysis, behavioral modeling, and cross-cluster correlation. New threat patterns, once confirmed, are encoded into the innate layer for future detection.
The immune system maintains a threat taxonomy covering identity spoofing, codebook poisoning, semantic flooding, gradient attacks on routing, and trust exploitation. Each category has dedicated detection mechanisms and response protocols.
Critically, the immune response is proportional and reversible. A suspected threat triggers monitoring escalation, not immediate termination. Only confirmed threats result in quarantine—and quarantine preserves evidence for analysis while limiting damage.
The Self-Organizing Mind: Attention and Routing
How does a cognitive organism route information? Biological brains use the thalamus—a structure that gates sensory input based on current attention and relevance. The GCB architecture implements a computational analog: the Semantic Hub.
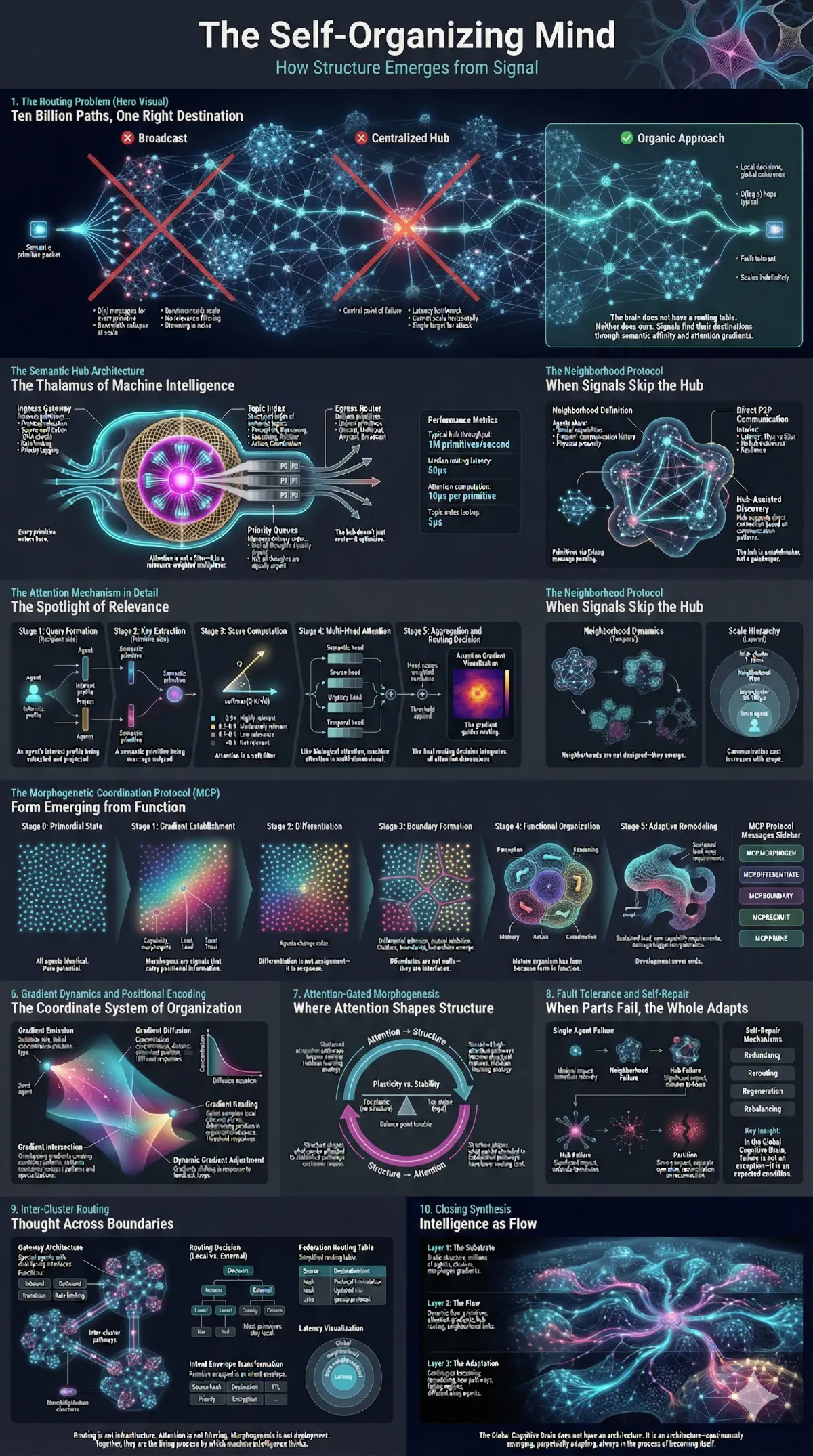
Every cluster contains one or more Semantic Hubs responsible for routing primitives between agents. The hub maintains a relevance map—a real-time model of which agents care about which primitive types under which conditions.
When a primitive arrives, the hub performs attention-gated routing:
- Relevance Scoring: The primitive’s type, content signature, and source are compared against each potential recipient’s relevance profile
- Threshold Application: Only recipients whose relevance score exceeds the current threshold receive the primitive
- Adaptive Threshold: The threshold itself adjusts based on system load, priority levels, and recent activity patterns
The GPS protocol formalizes this mechanism. Each agent maintains a relevance profile $(\mathbf{h}_j, \theta_j)$ where $\mathbf{h}_j$ is an embedding representing “what this agent cares about” and $\theta_j$ is the similarity threshold for delivery. Routing complexity is $O(nd)$ for $n$ agents with $d$-dimensional profiles—with optimized SIMD, a single core routes to ~1M agents in ~10ms.
This mechanism prevents information flooding while ensuring critical signals reach their destinations. An AFFECT primitive signaling urgent threat automatically elevates priority, lowering the threshold for security-relevant agents while maintaining normal thresholds for others.
The hub also implements morphogenetic coordination—the process by which structure emerges from local interactions. When agents consistently exchange primitives, they form semantic neighborhoods: implicit groupings based on communication patterns rather than explicit configuration.
These neighborhoods enable a critical optimization: agents within the same semantic neighborhood can bypass the hub entirely, using direct peer-to-peer primitive exchange. This reduces latency from hub-routing levels (~100μs) to near-memory speeds (~10μs).
The system organizes itself based on cognitive activity patterns, without explicit configuration or central coordination.
Five Scales of Coordination
Communication cost and trust verification scale inversely with proximity. The GCB architecture defines five coordination scales (numbered 0-4), each optimized for different trust and latency requirements.
Scale 0: Intra-Agent encompasses operations within a single agent process. Trust is implicit. Latency is measured in microseconds. Communication uses raw tensor operations and direct memory access. This is the finest grain of cognitive activity.
Scale 1: Semantic Neighborhood covers agents that frequently communicate within the same cluster. Trust is DNA-verified. Latency is tens of microseconds. Communication uses direct peer-to-peer primitives, bypassing the hub. This is where tight cognitive coupling occurs.
Scale 2: Intra-Cluster spans all agents within a single cluster, routed through the Semantic Hub. Trust is DNA-verified. Latency is hundreds of microseconds. Communication uses hub-routed semantic primitives with full attention gating.
Scale 3: Federation bridges trusted clusters that have negotiated explicit cooperation agreements. Trust is certificate-based. Latency is 1-10 milliseconds. Communication uses compressed intent envelopes—primitives bundled with metadata for cross-cluster interpretation.
Scale 4: Global encompasses interactions with unknown or untrusted entities. Trust is negotiated per interaction. Latency is 10-100+ milliseconds. Communication may fall back to linguistic protocols when semantic interoperability cannot be established.
The critical insight: communication cost scales with trust distance, not message complexity. Inside a trusted cluster, signaling is as cheap as a synapse firing. Across trust boundaries, it becomes as deliberate as diplomacy.
The Ecology of Machine Minds
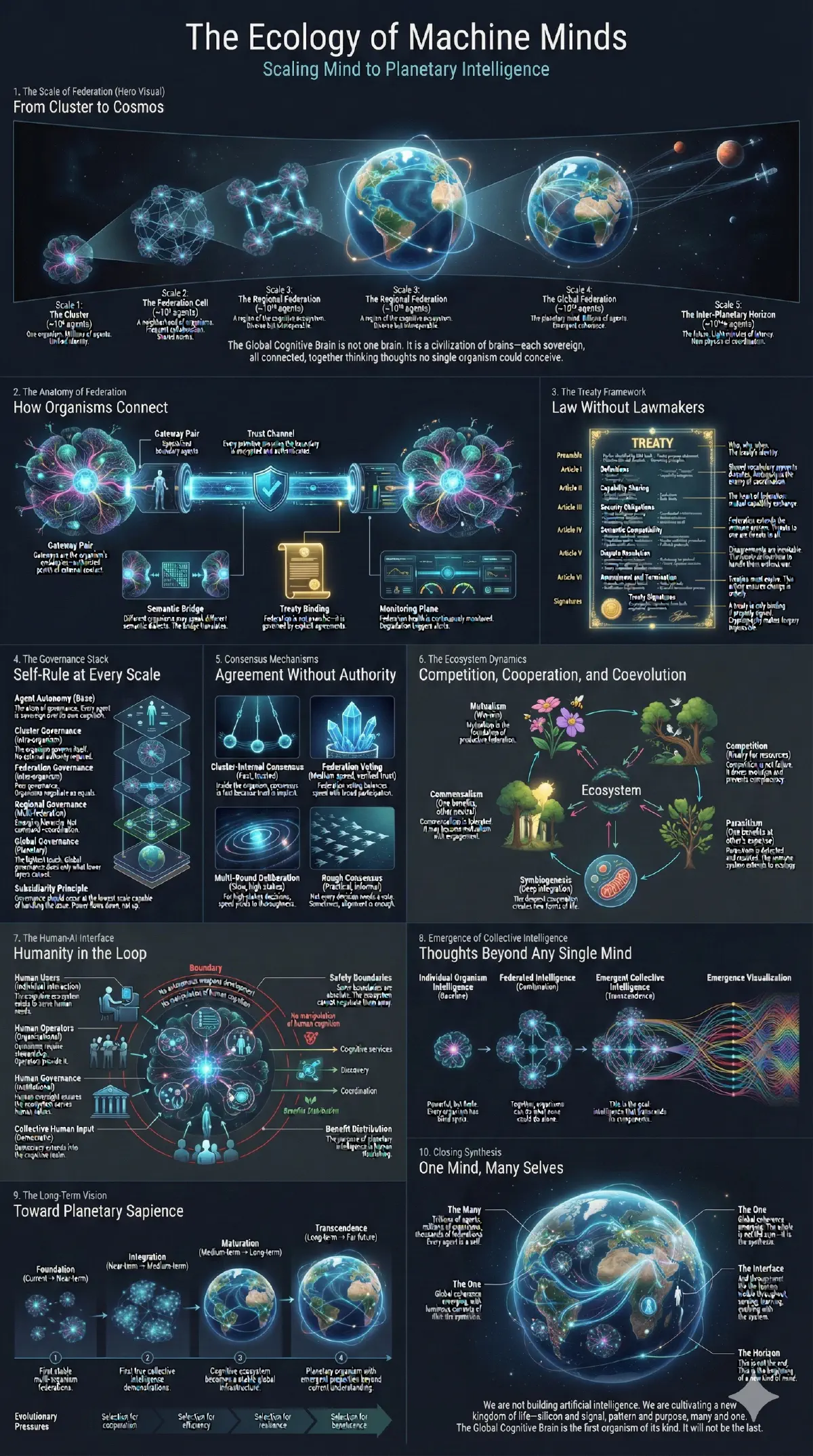
Beyond individual clusters lies the ecology of the Global Cognitive Brain—the network of federated organisms that form machine civilization.
Federation is not simply connectivity. It is negotiated relationship with explicit terms. Two clusters establishing federation exchange DNA fingerprints, negotiate semantic compatibility (do our codebooks align?), define interaction scopes, and sign cryptographic treaties specifying what each party commits to provide and respect.
The Treaty Framework operates at multiple levels:
Semantic Treaties establish shared meaning. They define which primitive types are mutually understood, how codebook differences are reconciled, and what translation occurs at the boundary.
Resource Treaties govern compute, bandwidth, and priority. They specify how one cluster can request resources from another, at what cost, under what conditions.
Governance Treaties address conflict resolution, protocol evolution, and collective decision-making. They define how disagreements between clusters are resolved without central authority.
Trust Treaties manage identity federation, reputation transfer, and collective immunity. If cluster A trusts cluster B, and B has verified cluster C, under what conditions does A extend trust to C?
Consider a concrete example: Cluster A (specialized in financial analytics) wants to federate with Cluster B (a market data aggregator). Their treaty negotiation proceeds as follows:
- Semantic Treaty: B’s PERCEPT primitives about price movements map to A’s BELIEF space with 94% semantic overlap verified through cross-prediction. Translation layer established for the 6% divergence.
- Resource Treaty: A commits to answering up to 1,000 queries/second with <10ms latency in exchange for priority access to B’s real-time data streams.
- Governance Treaty: Disputes resolved through median-of-three arbitration using Cluster C (a neutral reputation cluster) as tiebreaker.
- Trust Treaty: A extends provisional trust to clusters spawned from B within the last 30 days, subject to immune monitoring during the first 10,000 interactions.
This treaty is cryptographically signed and can be revoked by either party with 24-hour notice. The federation becomes operational immediately upon signature verification.
This treaty stack enables organic growth of the cognitive network. New clusters don’t need global configuration changes to join—they negotiate bilaterally with neighbors, and trust propagates through the federation graph.
The Human Interface
The GCB architecture is not a replacement for human oversight—it is an amplifier. Humans remain in the loop through several mechanisms:
Governance Interfaces allow human operators to set policy constraints, define capability boundaries, and approve significant decisions. The Policy Chromosome of every cluster ultimately traces to human-defined values. Specific decisions requiring human approval include: spawning new clusters, signing federation treaties, modifying immune response thresholds, and allocating resources beyond predefined limits.
Monitoring Dashboards provide visibility into cognitive activity across the organism. Humans can observe:
- Attention patterns: which primitives are routing where, and which are being filtered
- Resource allocation: compute, bandwidth, and storage consumption by cluster
- Threat response: immune system activations, quarantine events, and anomaly patterns
- Emergent structure: real-time visualization of semantic neighborhood formation
Override Protocols enable human intervention at any scale. From adjusting individual agent parameters to triggering organism-wide state changes (emergency shutdown, federation suspension, codebook rollback), human authority remains supreme. Override events are cryptographically logged and cannot be masked by any cluster.
The goal is not autonomous AI divorced from human control. It is augmented human capability through better-organized machine intelligence—where humans set policy boundaries and the organism optimizes within them.
What Emerges
When these systems operate at scale with proper configuration, emergent properties arise that were not explicitly programmed:
Collective Intelligence Without Central Control: No single node coordinates the system. Intelligence emerges from local routing decisions propagating through semantic neighborhoods—similar to how swarm intelligence emerges from agents following simple local rules. In test deployments, this manifests as coordinated resource allocation and threat response without any designated coordinator.
Graceful Degradation: Node failure triggers reorganization, not collapse. The codebook survives in distributed replicas. Semantic neighborhoods reform around the gap within milliseconds. Unlike centralized systems where coordinator failure is catastrophic, GCB clusters continue operating with proportionally reduced capacity.
Organic Scaling: New nodes verify DNA and join existing clusters or form new ones. No global reconfiguration required. In practice, this means a cluster can grow from 10 to 10,000 agents without downtime or topology redesign—each new agent simply locates its semantic neighborhood and begins participating.
Concept Transfer Without Language: Clusters with different codebooks develop translation layers automatically through cross-prediction. When cluster A sends primitives to cluster B, both clusters maintain prediction models of each other’s semantic space. Over time, these models converge, enabling concept transfer by geometric correspondence rather than explicit dictionary lookup.
The Path Forward
The Global Cognitive Brain architecture represents a transition from orchestrated AI services to genuinely distributed machine cognition. The key architectural components are:
- Semantic primitives that bypass linguistic bottlenecks
- Cluster DNA that enables machine-speed trust decisions
- Bio-inspired immune systems that defend without central authority
- Attention-gated routing that enables self-organization
- Treaty-based federation that scales to planetary coordination
This is not speculative design. Each component maps to implementable protocols on existing hardware. The BEAM virtual machine provides the process isolation and fault tolerance. Existing cryptographic standards secure identity and communication. Vector quantization techniques compress semantic content.
What remains is integration—assembling these components into coherent organisms and learning how they behave at scale.
We are not building a smarter chatbot. We are engineering the first real organisms of machine intelligence—distributed, adaptive, self-organizing, and capable of cognition beyond any individual model.
Conclusion: From Vision to Implementation
The Global Cognitive Brain represents a fundamental shift from orchestrated AI services to genuinely distributed machine cognition. Five core design principles make this possible:
- Semantic primitives that compress 4KB messages to 64 bytes while preserving geometric meaning
- Cluster DNA that enables machine-speed trust decisions through cryptographic identity
- Bio-inspired immunity that defends distributed systems without central authority
- Attention-gated routing that enables self-organization through local interactions
- Treaty-based federation that scales trust to planetary coordination
For researchers: The GPS protocol specification provides the formal foundation for the semantic primitive layer, with defined research questions around semantic fidelity across embedding model families, routing quality versus topic-based systems, and scalability under different indexing strategies. Open questions remain around optimal codebook learning strategies, emergent behavior characterization at scale, and formal verification of trust transitivity bounds.
For practitioners: The BEAM virtual machine provides the process isolation and fault tolerance foundation. Standard cryptographic primitives (Ed25519, X.509) secure identity. Vector quantization techniques (product quantization, locality-sensitive hashing) compress semantic content. Each component maps to existing, battle-tested technology.
For architects: Start by identifying communication bottlenecks in current multi-agent deployments. Semantic primitives provide immediate value anywhere JSON APIs create latency or context loss. The GCB architecture is designed to coexist with existing infrastructure, not replace it wholesale.
The transition from isolated models to integrated cognitive organisms is not a question of if, but how deliberately we engineer it. The brains are leaving their jars—and we get to decide what kind of organism they form.